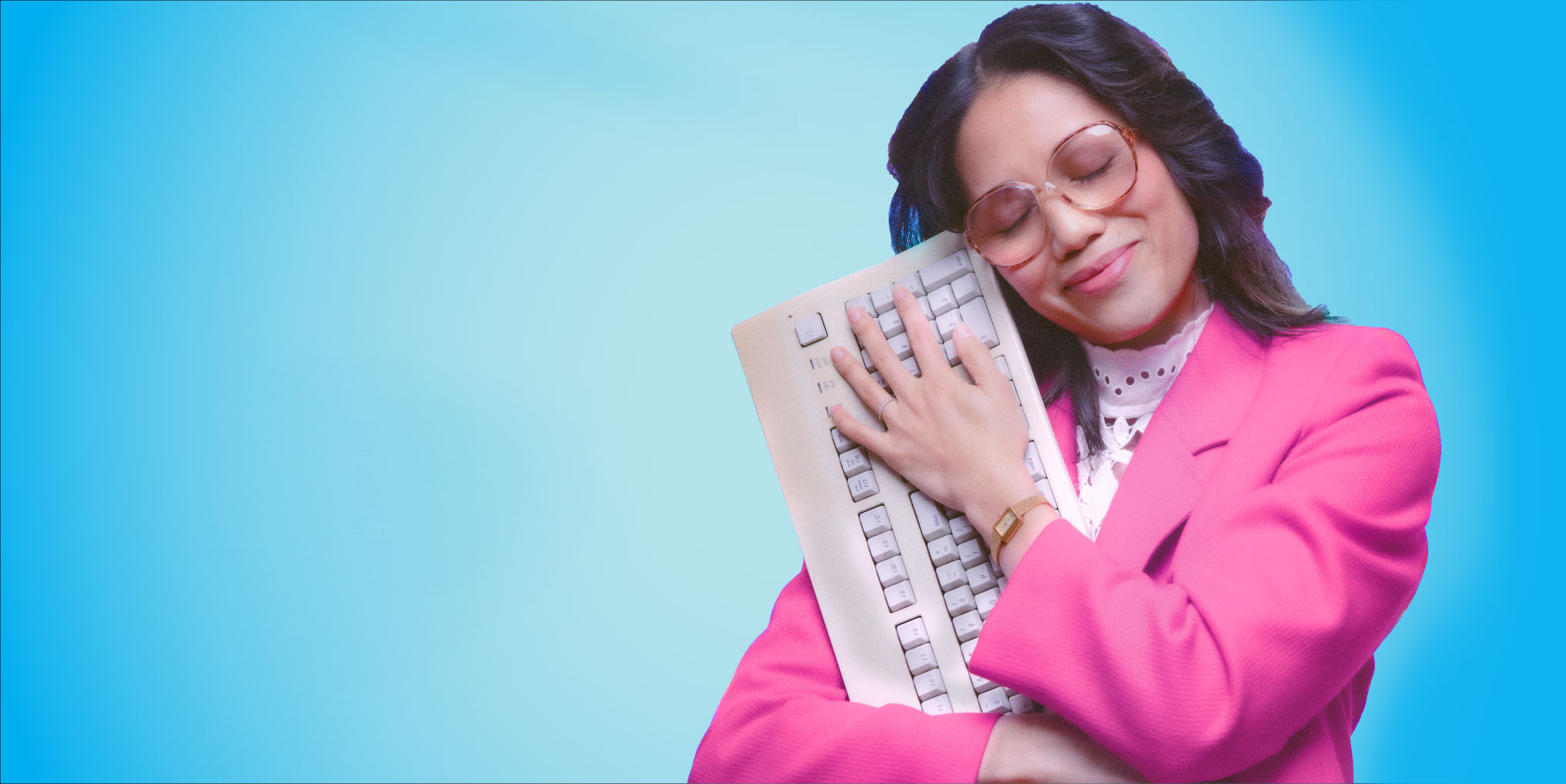
How we help organisations like yours_
As one of the UK’s leading Microsoft Partners, we’ve got the expertise to help you; break away from legacy tech, streamline your processes, get better value from your investment in the Microsoft stack. From large digital transformation projects to fully managed services and outsourced IT, we’ll help you level up your IT, systems, processes and objectives.